Blogs
Secrets Management using Mozilla sops


Introduction
As automation is taking place at a rapid pace, the areas where human intervention is involved are appearing as huge speed breakers. One such task is keeping the secret information with humans and providing necessary approvals as and when needed. This task does not involve a lot of logical thinking but the important aspect is keeping trustworthy information and using it for regular activity.
Keeping the secrets in a file and allowing access to information to a wider set of people will be a serious challenge. One way to solve this problem is to keep the secrets in a file but in an encrypted format and ensure only the target environment can decrypt. This way we can still allow the automation to happen and keep the environments secured.
In this blog, I will be touching upon the basics of securing secrets, introduce you to SOPS, explain to you how SOPS works and its effective use in building cloud-agnostic applications.
Reviewing the Basics
To understand how to effectively secure your secrets, we need to understand PGP (pretty good privacy) protocol. It is known as a military-grade encryption protocol available for general purposes. Below diagram depicts how PGP works:
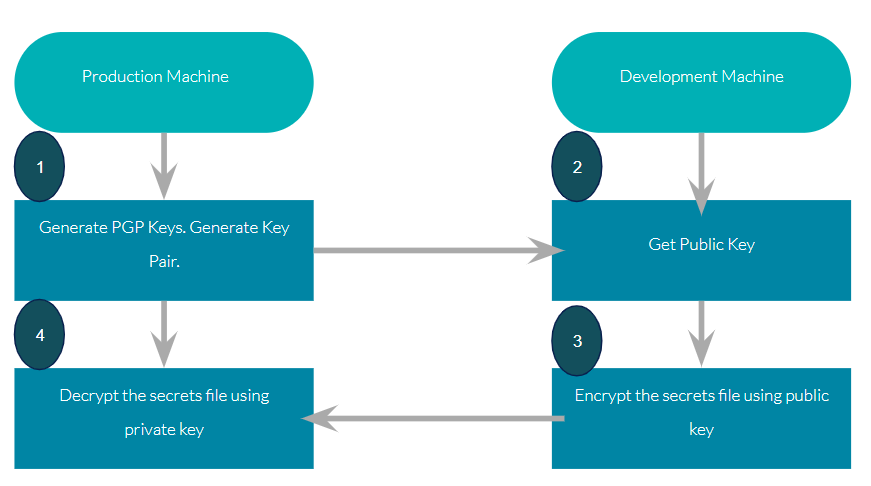
Assuming that you have a production environment and development environment. In development, you configure the secrets and encrypt them before the sharing of production. The production system will decrypt the files and use them.
The key point to note here is, the private key will always be in the production environment, hence there is no chance of decrypting files in any place, except in designated production machine..
Introduction to Mozilla SOPS
SOPS is an open-source tool from Mozilla which allows you to create and edit encrypted files. It supports encryption of a wide variety of file types i.e. YAML, JSON, INI and even binary files as well. You can find detailed documentation and source code here.
Encryption using SOPs
SOPS execution files are available in Windows, Linux and mac files. Download the sops based on your operating system from here. Once sops is installed, you need to create a .sops.yaml file which holds the public key(s). Here you should mention the public keys that are shared to you for encryption.
Sample .sops.yaml for AWS Key appears like below.
![]()
You can create a new encrypted secrets file using the following command.
![]()
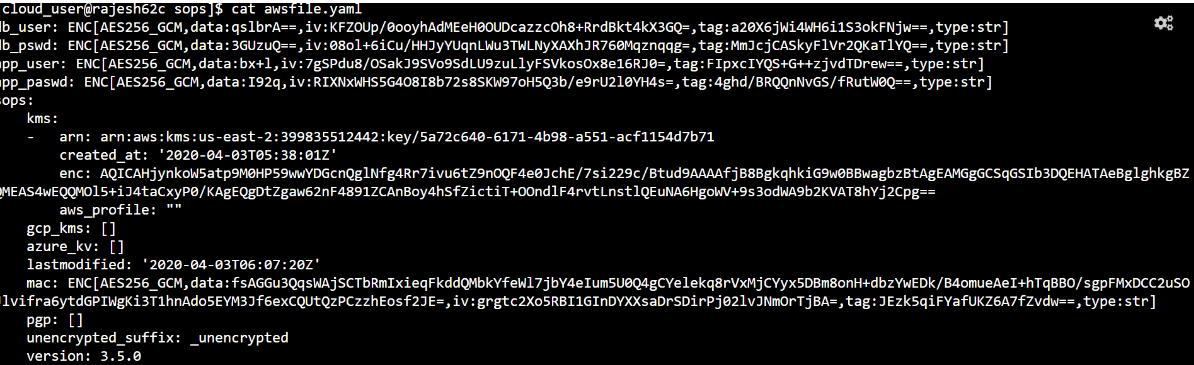
Encrypted secrets file will appear as below
The Problem of Bootstrapping Trust
In the ‘Revise Basics’ section, we talked about keeping the private key only in production specific machines and sharing the public key to the development team. This ensures security definitely, however production with a single machine is unimaginable these days. That means private key need to be distributed among multiple machines in production. This problem is effectively addressed by most of the cloud operators. I will take the example of AWS here. AWS has a KES feature. This allows you to generate key pairs and public keys are available to be shared. Private is not even displayed. But internally a private key is generated and it will be tagged to the role, all the production machines who have the role attached to machines get access to the private key and they can decrypt the secrets to perform required operations. Other clouds also have the more or less similar model in place
Cloud-Native behaviour of SOPS
SOPS works seamlessly with AWS, GCP, Azure and any private cloud. For private clouds, the encryption and decryption are driven through PGP. For other popular clouds, it works directly with specific key management solutions of each cloud.
Conclusion
SOPS is a simple yet effective tool for securing your secrets and the recommended choice if you are building products that are cloud-native. SOPS enables you to build applications which are cloud agnostic, secure and agile (Less human intervention).